BDD for the AI Era: Why we are evolving from Gherkin to Contracts
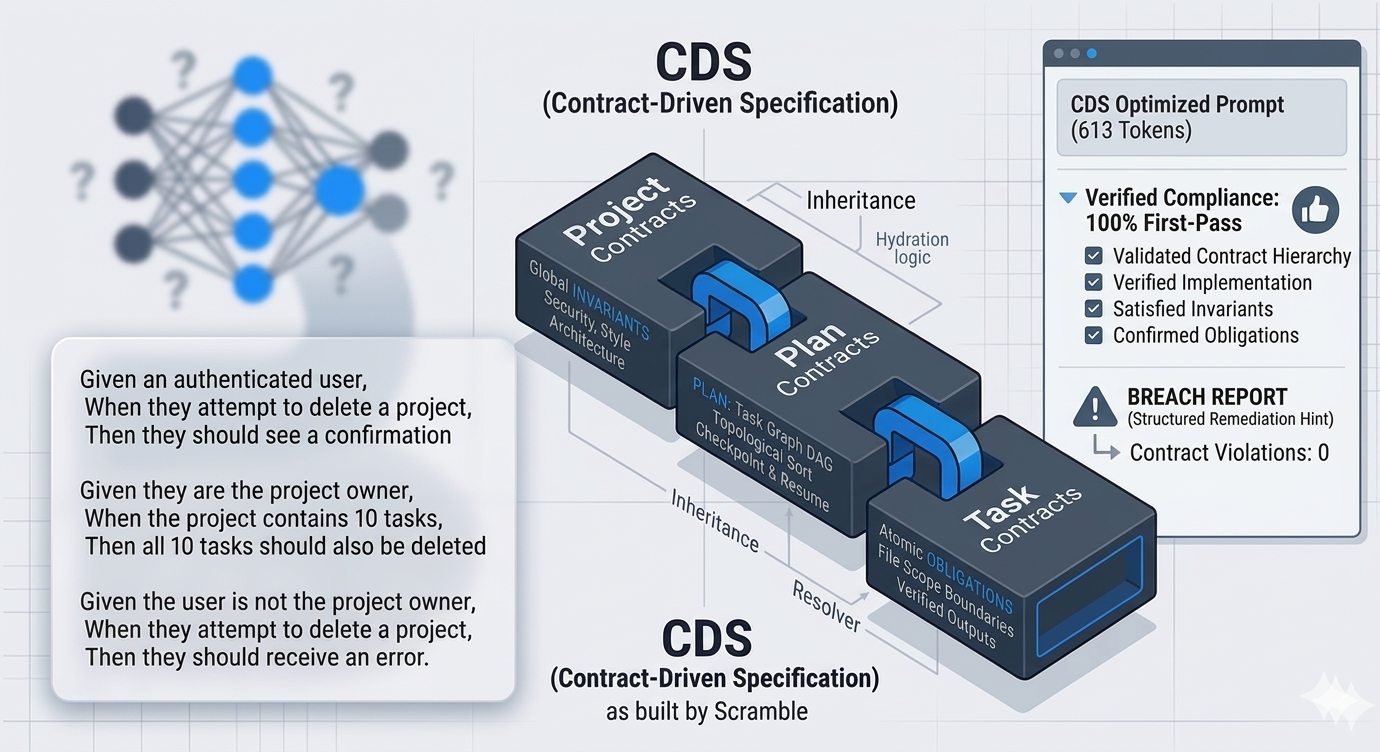
At Scramble, we are deep believers in Behavior-Driven Development (BDD). We love Gherkin.
Insights, updates, and stories from the Scramble Technology team.
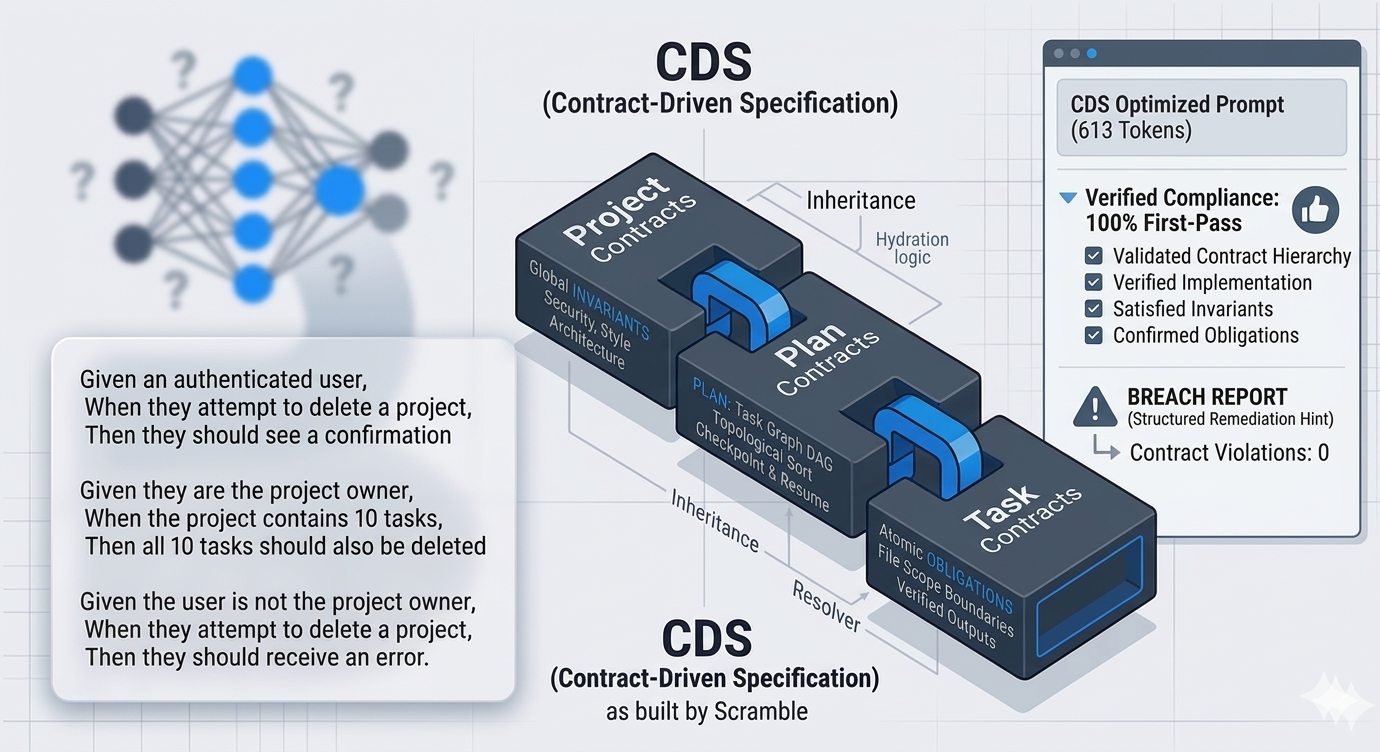
At Scramble, we are deep believers in Behavior-Driven Development (BDD). We love Gherkin.
There is a class of attack that does not require breaking your encryption today. It requires patience.

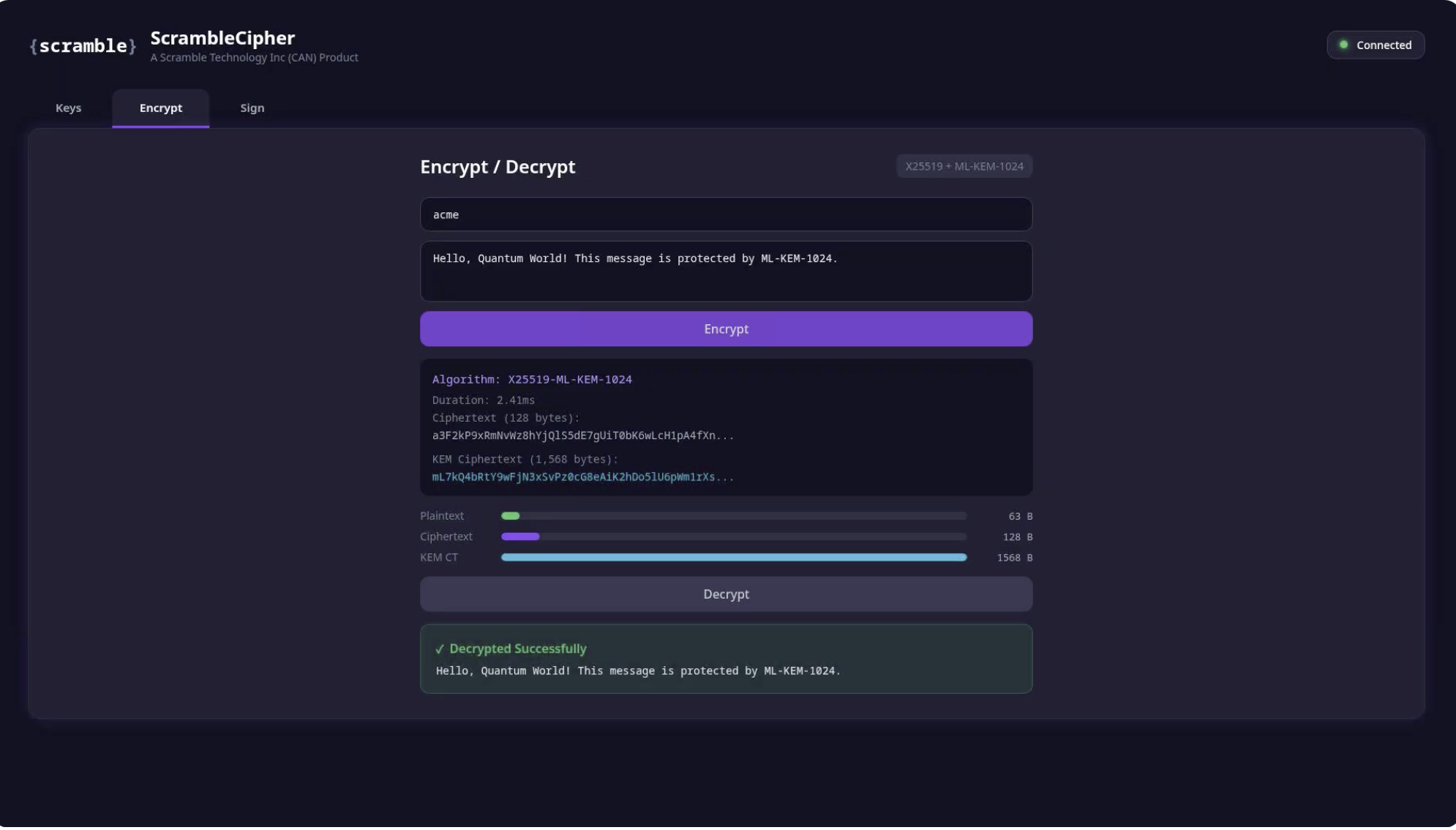
Every day, secrets move between your microservices thousands of times per second. A sufficiently powerful quantum computer running Shor's algorithm would break the encryption protecting that traffic. Adversaries already know this. They are recording encrypted data today, planning to decrypt it when quantum capabilities mature. This is the harvest now, decrypt later strategy, and the window for protection is now.

*In [Part 1](/blog/anatomy-of-a-quantum-attack-on-your-microservice-architecture-part-1), we walked through how a quantum-capable adversary harvests, break...

Quantum computers will break today's encryption. Learn how ScrambleVault uses NIST-approved hybrid post-quantum cryptography to protect your enterprise credentials now and in the future.
Get the latest posts and updates delivered to your inbox.