ScrambleCipher Beta Is Now Open
TL;DR
- If your team is handling sensitive data and wants to evaluate a stronger operational model for cryptography, you can learn more and join the beta here: Join the beta: ScrambleCipher Product Page Watch the demo: ScrambleCipher Demo Video Book a Discovery Call - ScrambleCipher was built to solve the operational side of modern cryptography, not just the algorithm side.
- The problem ScrambleCipher addresses is not encryption alone.
- It is the wider operational mess that surrounds it.
- That is the reason for the product, and it is the reason the beta is now open.
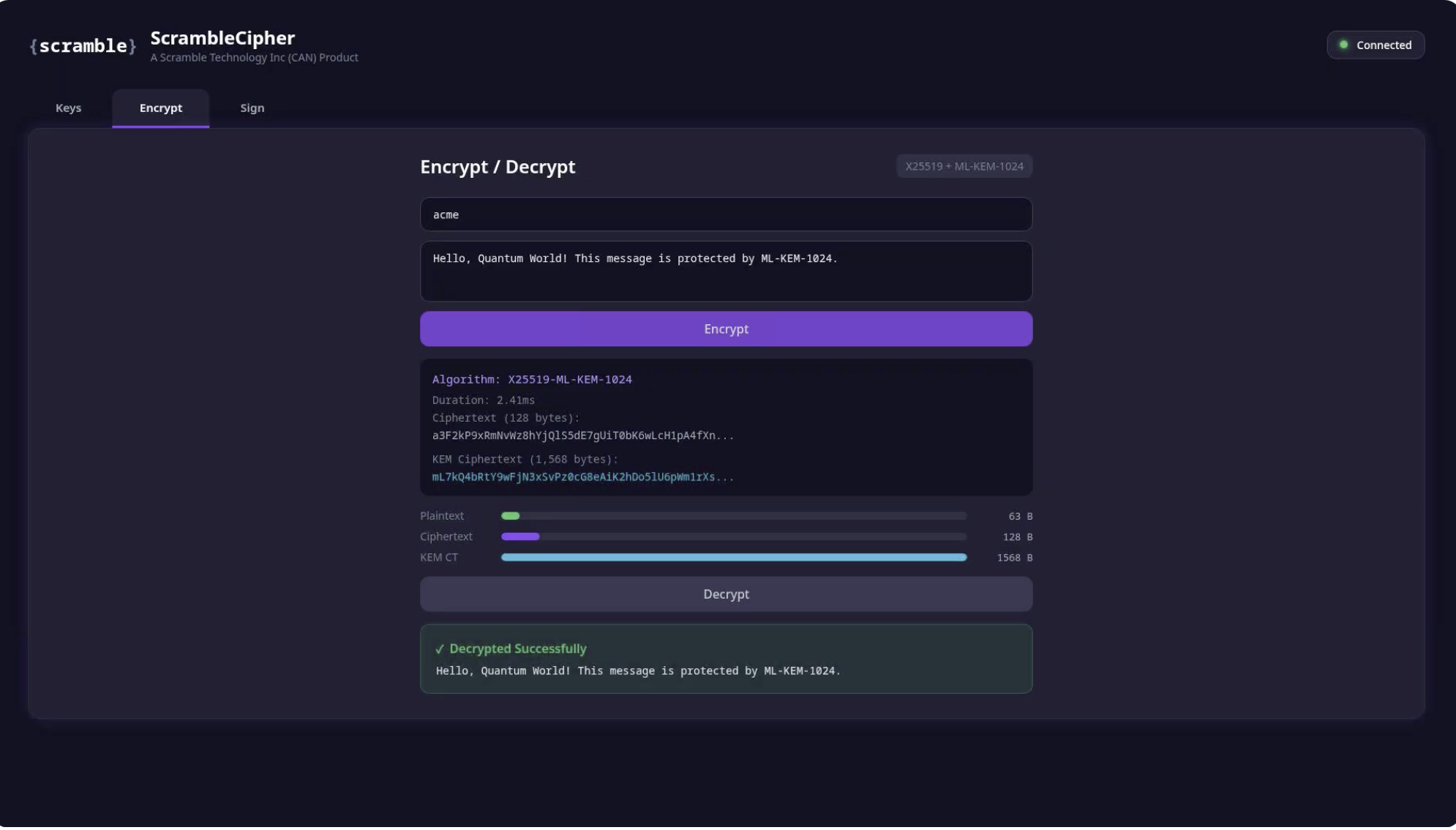
We have opened the beta programme for ScrambleCipher, a local cryptographic microservice built for teams that need stronger protection for sensitive application data and a more serious approach to key management.
The problem ScrambleCipher addresses is not encryption alone. It is the wider operational mess that surrounds it. Many organisations can add a cryptographic library to an application, but that does not mean they have solved the security problem. In practice, the harder questions begin after the algorithm has been chosen. Where are the keys stored? Who can access them? How are they rotated? What happens if one is compromised? How are backups protected? Can the organisation audit what was encrypted, signed, or verified, and by which key? These are the parts that often get bolted on late, handled manually, or left to application logic that was never designed to function as a secure cryptographic boundary.
That matters even more now because the risk is no longer confined to what an attacker can do today. One of the main drivers behind post-quantum cryptography is the threat commonly known as harvest now, decrypt later. The idea is simple and unpleasant. Encrypted data can be intercepted and stored now, even if it cannot yet be read. An attacker only needs to believe that future advances in quantum computing may make that data readable later. If the information still holds value at that point, the breach becomes retrospective. The compromise happened years earlier, quietly and without triggering alarm.
For organisations holding client records, legal material, financial information, private communications, internal business data, or any information with a long sensitivity lifespan, this is not the kind of problem that can be dismissed as theoretical. It raises a practical question for software teams and technical decision-makers: how do you strengthen encryption while also improving the way keys are handled in production?
ScrambleCipher was built to answer that question. Rather than embedding cryptographic operations directly into the main application runtime, it runs as a separate local service beside the application. Communication happens over a Unix domain socket, not over an exposed network interface. Key material remains outside the web application process. Keys are encrypted at rest. Access to the service is controlled locally. Rotation support, encrypted backups, authentication, and rate limiting are part of the design rather than afterthoughts added later. The intention is to give teams a more secure operational model, not just a new algorithm call.
The service uses a hybrid approach to cryptography, combining classical and post-quantum methods for key encapsulation and digital signatures. This provides a more practical path for organisations that want to begin preparing for post-quantum threats without throwing away the security assumptions and compatibility models they already understand. Just as importantly, integration is deliberately lightweight. Applications can communicate with ScrambleCipher over a simple JSON-based protocol, which makes it possible to integrate from PHP, Python, Node, Go, or any other language with socket support.
We have opened the beta because we want to work with teams that have real deployment intent and real data protection concerns. This is not aimed at people who simply want to play with a cryptographic novelty. It is aimed at organisations that understand the value of protecting sensitive information properly and want to evaluate whether a sidecar-style cryptographic service is a better fit than embedding key handling directly inside their application stack.
Teams interested in joining the beta can review the product, watch the demo, and book a discovery call to discuss their use case. We are particularly interested in speaking with organisations that want to test ScrambleCipher in practical environments and provide grounded feedback during the beta phase.
Join the ScrambleCipher Beta
If your team is handling sensitive data and wants to evaluate a stronger operational model for cryptography, you can learn more and join the beta here:
- Join the beta: ScrambleCipher Product Page
- Watch the demo: ScrambleCipher Demo Video
- Book a discovery call: Discovery Call
ScrambleCipher was built to solve the operational side of modern cryptography, not just the algorithm side. That is the reason for the product, and it is the reason the beta is now open.
Key Takeaways
- Just as importantly, integration is deliberately lightweight.
- Teams interested in joining the beta can review the product, watch the demo, and book a discovery call to discuss their use case.
- Rather than embedding cryptographic operations directly into the main application runtime, it runs as a separate local service beside the application.
- Communication happens over a Unix domain socket, not over an exposed network interface.
- Key material remains outside the web application process.
Share this post
Comments (0)
No comments yet. Be the first to comment!
Leave a Comment
Comments are moderated and will appear after approval.